A design flaw in Windows Smart App Control and SmartScreen that enables attackers to launch programs without triggering security warnings has been under exploitation since at least 2018.
Smart App Control is a reputation-based security feature that uses Microsoft’s app intelligence services for safety predictions and Windows’ code integrity features to identify and block untrusted (unsigned) or potentially dangerous binaries and apps.
It replaces SmartScreen in Windows 11, a similar feature introduced with Windows 8 designed to protect against potentially malicious content (SmartScreen will take over when Smart App Control is not enabled). Both features are activated when the user attempts to open files tagged with a Mark of the Web (MotW) label.
As Elastic Security Labs discovered, a bug in the handling of LNK files (dubbed LNK stomping), can help threat actors bypass Smart App Control security controls designed to block untrusted applications.
LNK stomping involves creating LNK files with non-standard target paths or internal structures. When a user clicks on such a file, explorer.exe automatically modifies the LNK files to use the correct canonical formatting.
However, this also removes the MotW (Mark of the Web) label from downloaded files, which Windows security features use to trigger a security check.
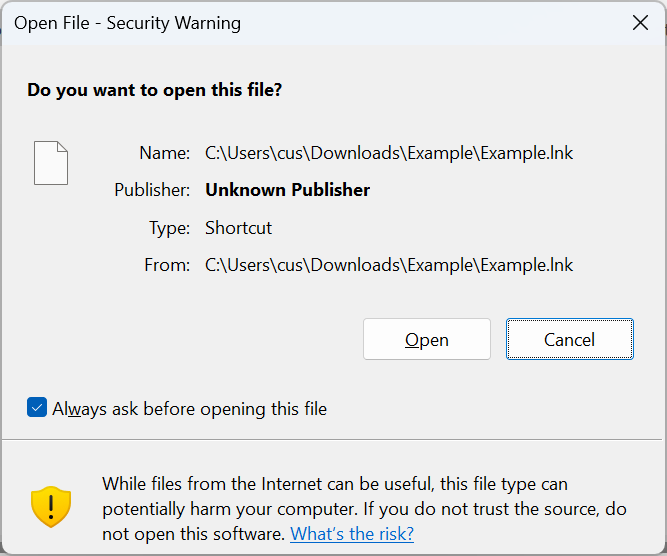
To exploit this design flaw, one can append a dot or space to the target executable path (for instance, after a binary’s extension like “powershell.exe.”) or create an LNK file containing a relative path, such as “.target.exe”.
When the user clicks the link, Windows Explorer will look for and identify the matching .exe name, correct the full path, remove the MotW by updating the file on disk, and launch the executable.
Elastic Security Labs believes this weakness has been abused in the wild for years, given that it found multiple samples in VirusTotal designed to exploit it, the oldest of which was submitted more than six years ago.
It also shared these findings with the Microsoft Security Response Center, which said the issue “may be fixed in a future Windows update.”
Elastic Security Labs also described other weaknesses that attackers can exploit to bypass Smart App Control and SmartScreen, including:
- Signed malware: signing malicious payloads using code-signing or Extend Validation (EV) signing certificates.
- Reputation hijacking: finding and repurposing apps with a good reputation to bypass the system.
- Reputation seeding: deploying attacker-controlled binaries onto the system (e.g., an application with known vulnerabilities or malicious code that triggers only if certain conditions are met).
- Reputation tampering: injecting malicious code in binaries without losing associated reputation.
“Smart App Control and SmartScreen have a number of fundamental design weaknesses that can allow for initial access with no security warnings and minimal user interaction,” Elastic Security Labs warned.
“Security teams should scrutinize downloads carefully in their detection stack and not rely solely on OS-native security features for protection in this area.
“We are releasing this information, along with detection logic and countermeasures, to help defenders identify this activity until a patch is available.”
Elastic Security Labs researcher Joe Desimone has released an open-source tool for checking a file’s Smart App Control trust level.
